Penetration Tests should be an important part of your company’s security strategy. Security experts – often external – try to find gaps in your IT infrastructures security. In this article we will explain what exactly penetration testing is and describe how it can be found in our portfolio.
Penetration testing (or pentesting) is a very comprehensive activity: it is about checking entire IT systems for vulnerabilities. Hereby, external experts test their clients security systems by mimicking an attacker. Where a malicious attacker aims to gain access to sensible data, take down infrastructure or escalate permissions . The ethical hacker uses the same methodologies and tools to simulate these attacks without any of the mentioned consequences
Pentesting – Goals and Procedures
Objectives of penetration tests are:
- Finding weaknesses in systems (e.g. as a result of an incorrect/insecure configuration)
- Finding weaknesses in applications (e.g. as a result of a logic flaw in the applications’ user authentication mechanism)
- Recommending specific improvement measures
- Certify the audited company
Companies that commission such a pentest want to protect their systems. Furthermore, they want to benefit from an outside view by learning what weaknesses their software and operational environment has.
A pentest usually comprises several stages:
- Together with the customer penetration test scope (and, optionally, a specific focus) are defined.
- Commissioned security specialists carry out the actual pentest. The pentest tool-supported automated test scenarios and manual attempts to identify security vulnerabilities.
- The penetration testers create a comprehensive report including details of the identified vulnerabilities and suggestions for remediation or mitigation.
- Final meeting: Presentation of results and recommendations, as well as a discussion of next steps, e.g. re-testing after remediation.
Of course, such a test is only a snapshot of the current systems’ security. However, identifying vulnerabilities and their causes (lack of know-how, gaps in the security hardening process, organizational weaknesses, e.g. missing / incorrect responsibilities) will help to reduce the likelihood of future security incidents occurring.
What can go wrong?
Penetration testing is able to discover a variety of potential security vulnerabilities. Addressing these is crucial to prevent serious consequences:
- Data exfiltration and data loss, i.e. an unauthorized person can copy and / or delete data. Besides legal and financial consequences, these incidents can lead to serious damage to a company’s reputation
- Unauthorized access through key theft
- Escalating privileges allowing outsiders or employees access to sensible systems and data
- Non-availability of applications due to targeted sabotage actions
- In the cloud environment: Employees who only require user rights to cloud applications having access to the internal company network due to incorrect configurations
Pentesting in Cloud Environments
Prior to running pentests in a cloud environment some critical aspects have to be considered. These extend beyond the configuration of the company’s cloud environment, due to sharing physical hardware and network resources with other companies. Hence, acknowledging terms and requirements of the cloud provider during planning and execution is recommended. AWS, provides important information on this topic. For example, AWS prohibits the execution of Denial-of-Service(DoS)- attacks with pentesting. The reason for these restrictions on cloud pentesting is as mentioned above, the fact that several companies can potentially share resources in the cloud. In the IaaS model, you have mere hardware resources for your exclusive use. With SaaS it can happen that a pentest also has an impact on the availability of services for other cloud customers. You should communicate and coordinate your plans with the cloud provider to prevent your pentests from having impact on other companies.
Penetration Testing by A&B
External security experts usually execute pentests. Classically, penetration testers would start a penetration test with network discovery to identify possible targets on the networks exposing OnPrem resources, following up by simulating attacks on any identified services. Such a classic vulnerability testing approach may not cover, or not sufficiently focus on, security vulnerabilities and attack vectors applicable to modern applications commonly running in the cloud. Single page apps backed by an API Gateway and serverless scripting require a different take at penetration testing, and a different approach for mapping resources. If your applications are running in an AWS environment, our experts at Alice&Bob.Company can help you in all areas of AWS Cloud Security, including, but certainly not limited to, penetration testing.
The following graphic illustrates the A&B customer journey:
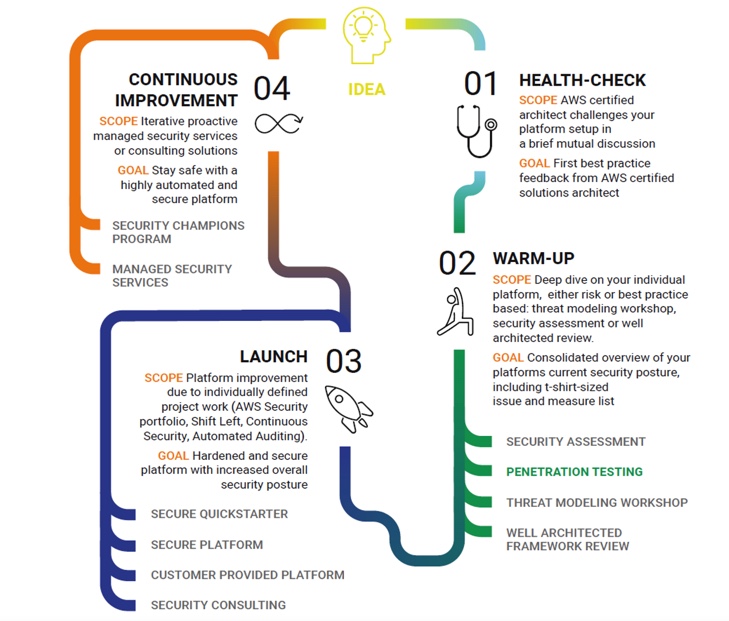
Penetration testing is part of our warm-up phase with the goal to receive a consolidated overview of the customers platform. In addition pentesting, our warm up phase includes the services: Security Assessment , Threat Modeling Workshop, Well Architected Framework.
If you are interested in more details on how A&B security experts carry out cloud penetration tests, have a look at our recent project with BLOXXON AG or contact us at Alice&Bob.Company!